Voice Assistants Have a Variety of Underlooked Vulnerabilities: Ultrasonic Commands, Cloned Voices, and Even Lasers - CPO Magazine
$ 5.99 · 4.9 (205) · In stock

New type of attack on voice assistants uses ultrasonic waves to access the devices through solid surfaces that are inaudible to humans without the use of special equipment.
News, insights and resources for data protection, privacy and cyber security leaders

Voice Assistants Have a Variety of Underlooked Vulnerabilities

Voice Assistants & Voice Computing – Cyber Security and Avoiding

Study Reveals Inaudible Sound Attack Threatens Voice Assistants
Top 8 Best Voice Cloning Software [2024 New]

Synthetic voice biometrics are a shifty chorus of fraud, requiring
/cdn2.vox-cdn.com/uploads/chorus_asset/file/9193255/Screen_Shot_2017_09_07_at_10.09.32_AM.png)
Inaudible ultrasound commands can be used to secretly control Siri
Uncovering the unheard: Researchers reveal inaudible remote cyber

Hear no evil: Near-ultrasonic attacks on voice assistants
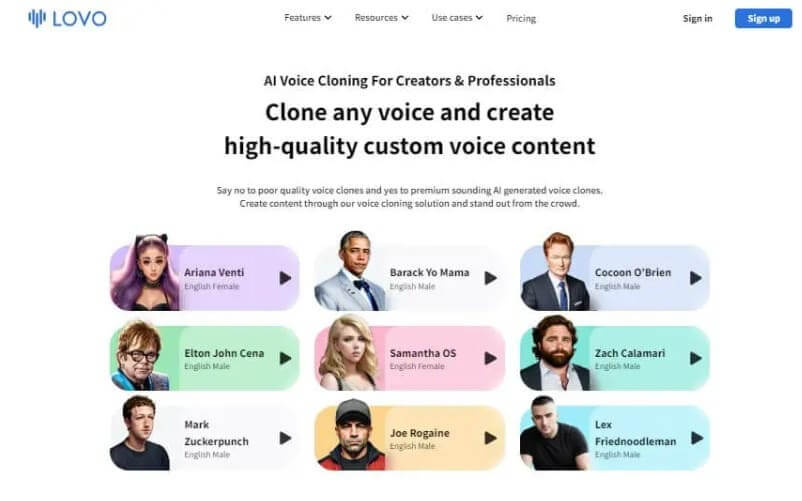
8 Best Voice Cloning Software Tools with High Quality 2023

Key Raises Issues of Hacking and Insurance Risks - CPO Magazine

Voicebot: A revolution in communication with voice assistants
.png)
Voice Search SEO: Everything you Need to Know
SWADE - Interface Zero 3.0 - The Players Guide To 2095
